Introduction
A data breach is an incident where an individual’s personal data is exposed or accessed by unauthorized parties. A data breach happens because of how personal data is collected, used, or handled; therefore, it is closely related to data processing under Law Number 27 of 2022 on Personal Data Protection(“PDP Law”). The introduction of the PDP Law in Indonesia brings significant changes to the governance of personal data processing. Under Article 16 paragraph (1) of PDP Law, personal data processing includes the entire set of activities involving data, from collection and acquisition, processing and analysis, storage, correction and updating, to display, disclosure, transfer, dissemination, as well as deletion or destruction.
Classification of Personal Data
Before discussing further, we need to understand that personal data is divided into two different categories under Article 4 paragraph (1) of the PDP Law, as follows:
| Specific Personal Data | General Personal Data |
| Article 4 paragraph (2) of the PDP Law | Article 4 paragraph (3) of the PDP Law |
| “health data, biometric data, genetic data, criminal records, children’s data, personal financial data, and other data in accordance with the provisions of laws and regulations.” | “full name, gender, nationality, religion, marital status, and data combined to identify a person.” |
Legal Basis for Personal Data Processing
The PDP Law regulates several legal grounds that can be used in processing personal data:
1. Contractual Obligation: Article 18 paragraph (2) of the PDP Law provides that a data controller may process personal data as long as it is necessary for the performance of a contract involving the data subject.
2. Legal Obligation: Under Article 37 in conjunction with Article 50 paragraph (1) of the PDP Law, data controller may also process personal data to fulfill applicable legal obligations. For example, banking institutions are required to prevent money laundering and fraud, so processing or verifying personal data may be carried out without the knowledge of the data subject as long as it is necessary to fulfill such obligations.
3. Legitimate Interest: Article 17 paragraph (1) of the PDP Law provides that personal data processing may be carried out based on legitimate interests as long as it is done proportionally. For example, companies may use CCTV recordings for security purposes, as long as it does not violate the rights of the data subject.
Understanding the Roles and Obligations of Data Controllers and Data Processors
The distinction between a data controller and a data processor is a key concept under the personal data protection law. This concept was previously recognized under Law No. 11 of 2008 on Electronic Information and Transactions, as amended by Law No. 1 of 2024 (“ITE Law”), where parties that process or manage data through electronic systems are generally referred to as Electronic System Operators (“PSE”). More specific terms such as Data Controllers and Data Processors were only clearly defined under the PDP Law. However, it is important to note that the definitions of PSE and Personal Data Controller are different in scope and legal function. In simple terms, a data processor handles personal data on behalf of a data controller and must follow the controller’s instructions. Meanwhile, a data controller decides why and how the data is processed, and therefore carries the primary responsibility.
If a data breach occurs, the obligation to report it rests with the data controller. Thus, the data controller must ensure that personal data is handled properly from the outset. This includes obtaining a valid consent before processing any personal data and providing a clear, transparent information about how the data will be used. This information is usually set out in a privacy policy, which should also explain the rights of the data subject, such as the right to access, correct, or request deletion of their personal data.
Application of Data Controller Responsibilities in Practice
After understanding the obligations of data controllers and data processors in obtaining consent from data subjects, it is important to examine how these obligations are applied in practice, particularly in the event of a data breach.
In May 2023, Bank Syariah Indonesia (“BSI”), acting as the data controller, experienced a major cyberattack that disrupted its mobile banking and ATM services for nearly a week. BSI stated that the disruption was caused by system maintenance. However, on 14 May 2023, it was revealed that the incident was the result of a ransomware attack carried out by the LockBit hacker group, which allegedly accessed and compromised customer data, including personal identities, account information, and financial transaction records.
In response to the incident, BSI focused primarily on service recovery and public communication regarding operational disruptions, while concerns were raised over the absence of clear and direct notification to the affected customers regarding the scope of compromised personal data. This drew public attention because, under Article 46 paragraph (1) of the PDP Law, a data controller is required to provide written notification to data subjects and relevant authorities within 3 x 24 hours in the event of a personal data protection failure. The incident also intensified public scrutiny over BSI’s compliance with its obligations as a data controller under Indonesia’s personal data protection framework
What Should Be Done When a Data Breach Occurs? [shown below]
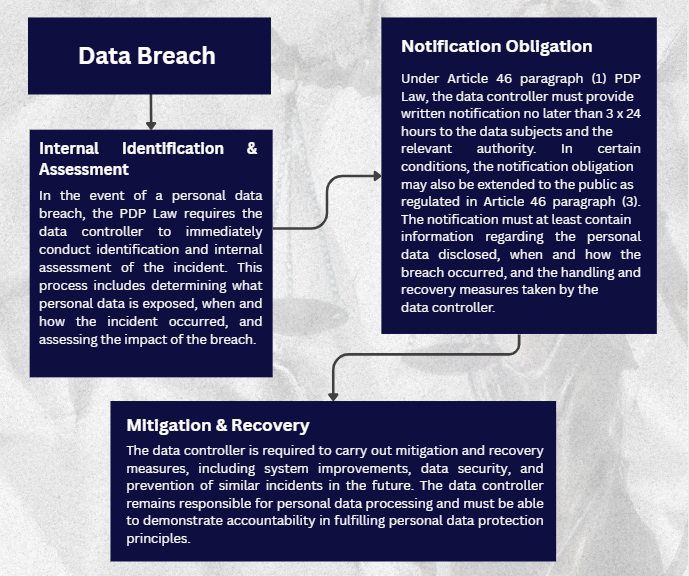
In the event of a personal data breach, every data controller is required to take specific mandatory steps under the PDP Law. To provide a clearer overview of the required legal and practical response, these steps are outlined in the following flowchart.
Conclusion
With the enactment of the PDP Law, all companies that process personal data are required to ensure that all personal data processing is carried out on a valid legal basis, supported by a proper consent, and aligned with the principles of transparency and accountability. In addition, companies should establish strong data protection and response mechanisms, including clear procedures for handling potential data breaches. These measures are essential not only to minimize legal risks but also to maintain and strengthen user trust.




